Protect On-Premise and Cloud Servers
Antivirus and EDR tools were not designed to protect servers, and application controls are insufficient to secure against advanced attacks. According to Gartner’s Cloud Workload Protection Platform (CWPP) recommendation, it is more essential for organizations to implement a zero trust run-time protection solution over AV/EDR to remove the risk of malicious code executing on servers that span across on-premise, virtual machines and containers.
Enter our solution for Windows Servers & Workloads. Secure your most critical assets, whether they run on-premise, cloud, or hybrid.
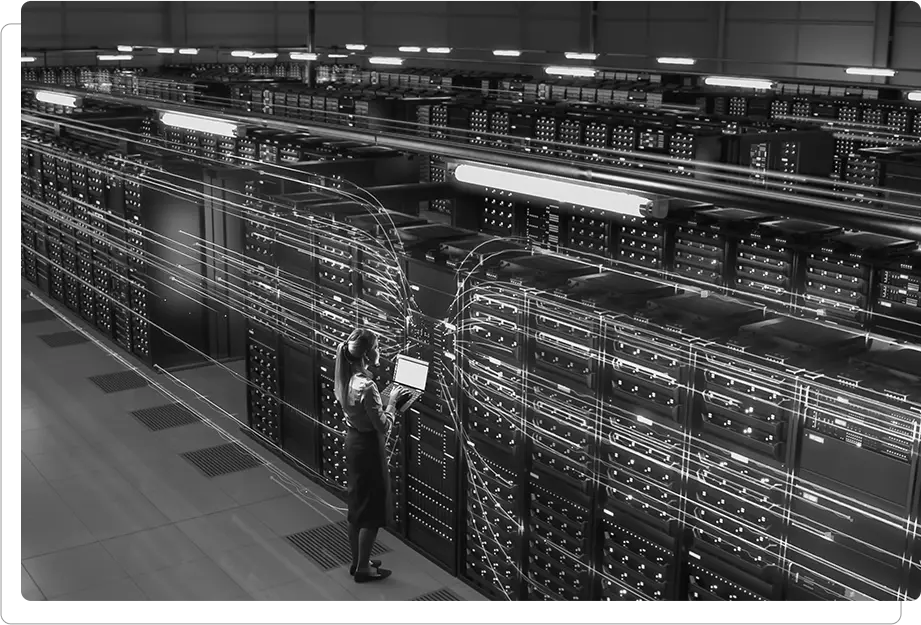
Protect Your On-Premises and Cloud Servers
Whether your servers run in your own datacenter or on a public cloud, they need protection against advanced cyberattacks. Security doesn’t need to cost you server performance or IT time. Our solution for Windows Servers & Workloads adds a dedicated memory defense layer for maximum server protection with minimal impact and effort.
- Secures on-premise and cloud server workloads, including AWS EC2 and Azure workloads via a single lightweight agent
- Provides zero trust in-memory runtime protection against supply chain attacks
- Prevents cyber attacks on administrators, including zero-day attacks, fileless attacks, evasive unknown malware and browser-based attacks
- Stops lateral movement breaches at the earliest stages, before they can gain access to your network
- ProtectWindowsservers with revolutionary, patented Moving Target Defense technology
- Blocks supply chain attacks that target mission critical applications and application upgrades
- Secure virtual application servers with no slowdown in performance, and no updates needed
- Captures rich, actionable forensic information for use by security teams and SIEMs
- Functions seamlessly across virtual, physical or hybrid IT environments
Secure Servers & Workloads Across Attack Vectors
Secure Servers & Workloads Across Attack Vectors
Our solution prevents browser, document, and supply chain attacks that target servers during admin logon sessions.
Lateral Movement
Our solution stops attackers moving laterally from a workstation to a server, from server to server, or from workload to workload.
Virtual Applications
Our solution’s lightweight agent means virtual apps can be secure without memory constraints

Moving Target Defense for Maximum Protection
Zero Trust Execution technology, powered by moving target defense, morphs the runtime environment, allowing authorized code to run safely while malicious code is deterministically blocked and trapped. It prevents evasive attacks, zero-days and attacks targeting known but unpatched vulnerabilities within whitelisted applications. It does so in a deterministic manner, without generating alerts to be analyzed, via a lightweight, easy to install 3MB agent requiring no administration.
Secure Virtual Application Servers
Most endpoint security solutions require updates and consume CPU resources that make them unsuitable for virtualized environments, while virtual application vendor security solutions don’t provide enough protection. At the same time, virtual environments face substantially more risk as more people in various roles have access to the server, thereby increasing the threat exposure


Simple to Rollout and Operate
Our solution is rapidly deployed through the cloud, with rollout measured in hours and days. The solution requires near zero maintenance and needs no configuration or tuning, ensuring very low ongoing costs. There is no monitoring or collection of personal data, a big plus for privacy aware companies
As it does not generate false positives, there is no associated alert fatigue or wasting resources on attacks that never occurred. It is extremely lightweight and does not require updates, making it optimal for virtualized environments.
Key Benefits
Prevent Advanced Unknown Threats Instantaneously
Prevents zero-days, ransomware, in-memory, and fileless attacks against Windows and Linux servers with no need for knowledge of threat form, type, or behavior.
Set and Forget Server Security
Quick and easy deployment, near zero maintenance and no system conflicts.
Cut Operational Costs
Does not generate false alerts, no need to investigate, analyze or remediate.
Extremely Lightweight
Light stateless agent with 2 Mb footprint, no run-time components and zero performance impact.
Maintain Business Continuity
Minimizes organizational risk while preserving ongoing operations with no interruptions for updates or scans.
Virtually Patch Vulnerabilities
Keeps your servers protected from vulnerability exploits when patches are not yet available or deployed.
See our solutions in action through interactive demos
Get a firsthand experience of how our products and platforms can fortify your defenses against modern cyber threads.
