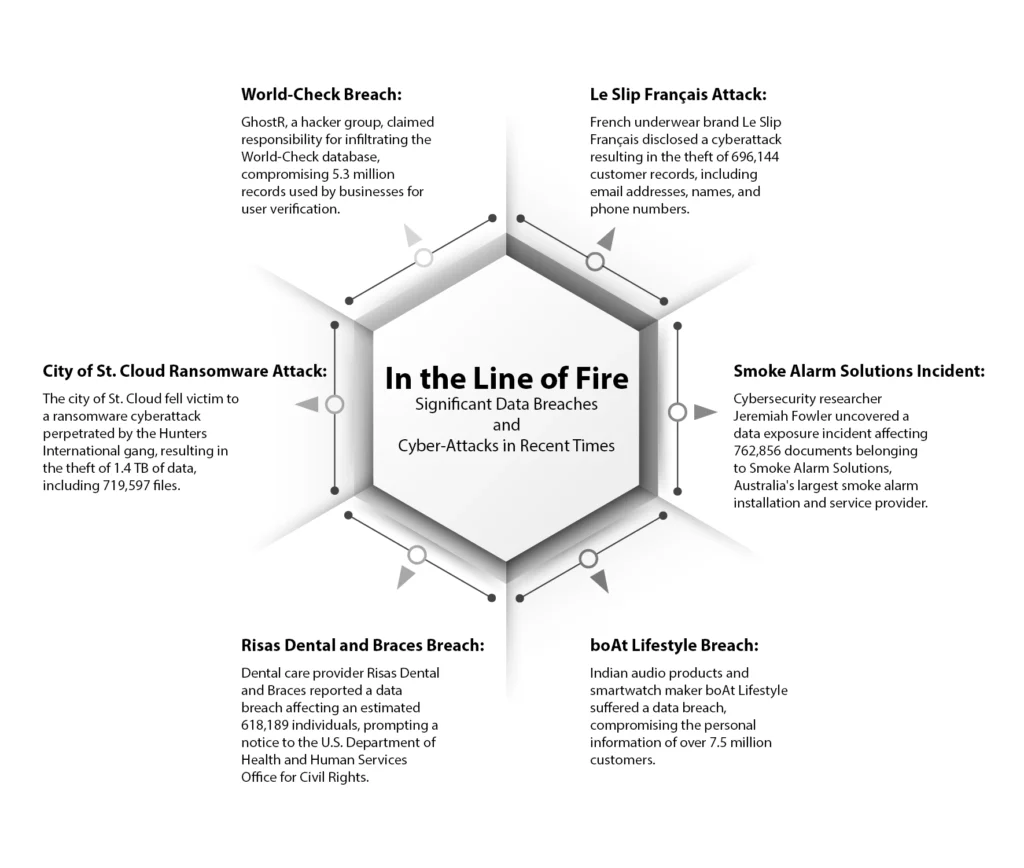
In recent months, the world has witnessed a series of significant data breaches and cyber-attacks that have reverberated across various industries and communities.
These incidents serve as poignant reminders of the omnipresent threat posed by cybercriminals and the indispensable importance of robust cybersecurity measures.
From multinational corporations to government agencies and healthcare providers, no sector has been immune to the fallout of these breaches. The breaches have laid bare sensitive personal information, financial data, and even classified government documents, underscoring the extensive repercussions of cyber-attacks.
This infographic highlights some significant breaches: